Choosing the Right SOC 2 Auditor: Why Experience and Judgment Still Matter

In today’s marketplace, a SOC 2 report is no longer a specialized report reserved for a handful of technology companies. For many organizations, particularly SaaS providers, fintech platforms, health‑tech companies, and technology‑enabled service organizations, it has become a baseline expectation from customers and business partners.
While these tools can play a helpful role in organizing evidence and tracking progress, organizations should pause before equating speed and automation with assurance. A SOC 2 report is ultimately an independent attestation over management’s description of a system and the effectiveness of controls.
This is where the choice of auditor matters and plays a critical role in helping organizations achieve meaningful, reliable assurance.
First, a brief SOC primer
There are a few types of SOC reports, with the most common being SOC 1® and SOC 2®. SOC 1 reports evaluate controls relevant to financial reporting and are common for payroll processors, financial institutions, and service providers that impact customers’ financial statements. SOC 2 reports evaluate controls related to the Trust Services Criteria (Security, Availability, Processing Integrity, Confidentiality, Privacy). They are most common for SaaS companies and technology service providers that handle customer data.
This article focuses on SOC 2 reports and the key considerations for ensuring you are engaged with a reliable partner for your systems assurance.
Download our guide to selecting the right SOC report for your company
SOC 2 is about assurance, not just compliance
At its core, a SOC 2 engagement is designed to provide confidence: confidence for management that controls are designed and operating as intended, and confidence for user entities that they can rely on those controls when outsourcing critical processes or data. Achieving that objective requires more than mapping controls to a checklist.
Experienced SOC 2 auditors understand that every organization’s system is unique. Infrastructure architecture, third‑party dependencies, software development practices, and operational maturity all influence how controls should be designed and evaluated. Applying professional judgment, particularly in areas such as scoping, risk assessment, and control precision, is essential to producing a report that accurately reflects the organization’s control environment.
Professional advisors with deep SOC experience bring this judgment to every phase of the engagement, helping ensure that the resulting report is not only in alignment with AICPA standards, but also meaningful and defensible.
Start a conversation with one of our SOC specialists
The growing sophistication of SOC 2 readers
Another important shift in the SOC 2 landscape is happening on the demand side. User entities are becoming more educated in how to read SOC 2 reports. Procurement teams, internal audit functions, risk and audit committees, and information security professionals increasingly scrutinize not just the opinion, but the details of the report itself.
Today’s readers pay close attention to:
- The clarity and completeness of the system description;
- Whether controls are sufficiently precise to address stated risks;
- The nature and timing of testing procedures; and
- The consistency between control descriptions, testing results, and exceptions.
As this sophistication grows, so does the risk of a report that appears superficial or overly standardized. A low‑cost or accelerated report that lacks depth may technically exist but still fail to satisfy customer due diligence.
An experienced auditor anticipates how reports will be read and used in practice and applies a level of rigor that stands up to this increased scrutiny.
The limits of automation and one‑size‑fits‑all approaches
Compliance tools can be valuable accelerators. They help centralize documentation, manage workflows, and provide visibility into readiness efforts. However, there are important limitations to what automation alone can address.
Automated platforms cannot:
- Assess whether a control is appropriately designed given a company’s specific risk profile;
- Exercise judgment when controls evolve mid‑period;
- Challenge management when a control exists in form but not in substance; or
- Interpret deviations in control design or operation in the context of overall system risk.
These decisions require experienced and appropriately knowledgeable professionals who understand both the technical requirements of SOC 2 and the operational realities of modern technology environments. A strong audit firm uses tools as inputs, not substitutes, for professional skepticism and analysis.
What experienced SOC 2 auditors bring to the table
Selecting the right auditor means selecting a team that understands how controls operate in the real world and within your organization.
That depth of experience and practicality translates into tangible benefits for clients, including:
- Thoughtful scoping which aligns the report with how the system is actually used;
- Clear, accurate system descriptions that withstand external review;
- Control testing that reflects both design and operating effectiveness (depending on report type);
- Early identification of issues that could impact the opinion or report usability.
Rather than treating SOC 2 as a transactional exercise, experienced auditors approach it as a collaborative process focused on long‑term trust and reliability.
Start a conversation with one of our SOC specialists
Supporting management, not just issuing a report
A well‑executed SOC 2 engagement also provides value beyond the final report. Management gains insight into control maturity, operational gaps, and areas where additional discipline or documentation may be warranted.
Importantly, this does not require an adversarial relationship. The most effective SOC 2 engagements strike a balance between independence and practicality, helping management understand expectations while maintaining the objectivity required for an attestation engagement.
This balance is difficult to achieve without a seasoned audit team that understands both the standards and the business context in which they are applied.
 Choosing an auditor with the end reader in mind
Choosing an auditor with the end reader in mind
As the SOC 2 marketplace continues to evolve, organizations will continue to see a range of options promising faster and lower cost results. For some organizations, these tools may serve as a useful starting point. However, when the objective is to deliver a report that stands up to real world scrutiny, the experience and judgment of the auditor remain central to the outcome.
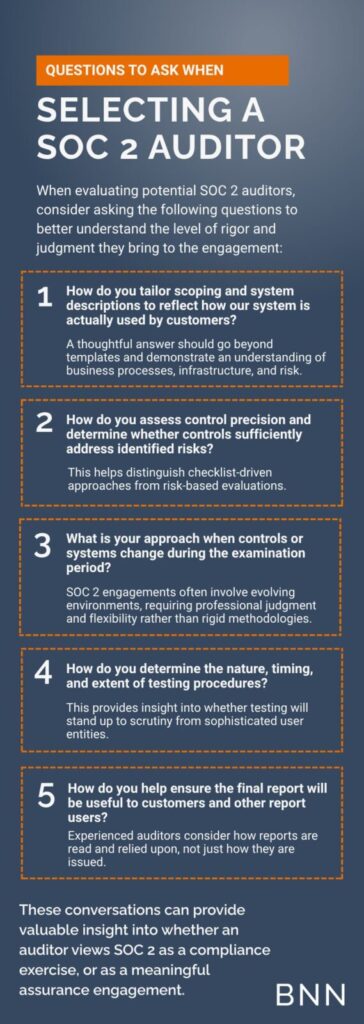
Organizations evaluating their SOC 2 approach should consider not only how a report is produced, but how it will be read, interpreted, and relied upon by customers and other stakeholders. Will this report help you win new business or deter potential customers? Asking the right questions about scoping, testing rigor, and auditor experience can mean the difference between a report that simply exists and one that genuinely builds trust. For a practical shortlist of questions to ask prospective auditors, see the sidebar: Questions to Ask When Selecting a SOC 2 Auditor.
If you have any questions or would like to discuss SOC 2 reports further, please contact Zach Porter.
Ready to learn more?
The Baker Newman Noyes Information Systems & Risk Assurance team combines deep technical expertise with practical judgment to tailor each SOC 2 engagement to how a system actually operates. We work closely with management from readiness through reporting, providing continuity, visible leadership involvement, and recommendations grounded in experience so the resulting SOC 2 report delivers meaningful assurance that customers and other stakeholders can confidently rely on.
With the BNN ISRA team, you will receive:
- Comprehensive guidance throughout the entire SOC 2 process, from initial readiness assessments to the ongoing completion of your Type 2 reports.
- Realistic recommendations tailored to your business needs.
- Access to the managers and principals who are performing and reviewing your work; we are accessible throughout the process and will address inquiries immediately and share relevant industry insights regularly.
Disclaimer of Liability: This publication is intended to provide general information to our clients and friends. It does not constitute accounting, tax, investment, or legal advice; nor is it intended to convey a thorough treatment of the subject matter.